Protect your people, processes and technology with managed detection and response (MDR).
Gain around-the-clock security protection and response using our best-in-class endpoint detection and response (EDR) software.

Managed detection and response is a proactive method of threat prevention.
Best-in-class technology combined with our SOC resources, advanced analytics and threat intelligence — plus extensive expertise in incident investigation and response processes — our managed detection and response services ensure your endpoints are protected, regardless of location.
Continuous Monitoring
Around-the-clock monitoring for suspicious activity and attempts to gain access into your organization’s system.
Proactive Detection
Actively looking for security threats to prevent breaches, disruptions and damages through improved visibility and detection.
Immediate Response
Expert alert and incident investigation as well as threat response processes and services helping to reduce time and impact.
Professional Protection
Security experts defend your company against threats, so you don't need to add internal resources.
Shield your people. Secure your process. Safeguard your technology with MDR.
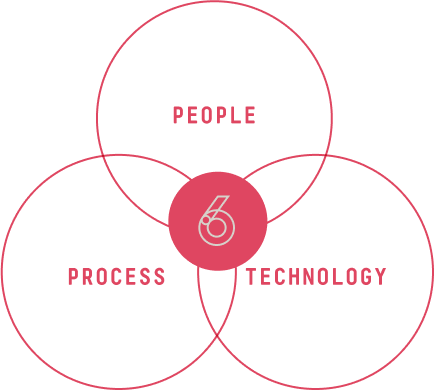
People
- Incident responders experienced in developing effective security programs.
- Senior badged resources focused on maturing and protecting our customers.
- Supportive representatives committed to active and meaningful communication.
Process
- Platforms that achieved top results in the MITRE ATT&CK testing.
- Advanced threat intelligence resources for enrichment.
- Additional automation and response platform for improved speed and efficiency.
Technology
- Threat validation via threat intelligence, behavioral analysis and other indicators.
- Efficient investigative processes to ensure accuracy of incidents and reduce mean-time-to-remediation (MTTR).
- Proven investigative processes for accurate, timely response.

A proven approach
We fully administer, support and operate your MDR services
Platform Administration
Following MSS best practices, Inversion6 provisions the Client’s site within the platform, the Group within the client’s site and the Group policies and exclusions.
Deployment Support
Inversion6 assists with deployments by providing deployment instructions, installation media and groups token for exclusion during deployment.
Security Operations
Inversion6’s state-of-the-art security operations center offers 24/7/365 monitoring, investigation and response. We implement the application of new indicators of compromise (IOCs) and threat hunting. Our co-developed run books for aim for improved response.

Implement MDR before it’s too late.
We can create a security program aligned with your organizational goals—not cookie-cutter.

MDR
VS
XDR
XDR evolved from the realization that a single perspective to monitor infrastructure is insufficient.
XDR provides advanced threat detection capabilities from various sources such as endpoints, networks, cloud services, and human errors, enabling Inversion6’s SOC team to rapidly detect and respond to security incidents before they can cause significant damage.
Choose MDR if your organization:
- Needs threat detection and response for endpoints and networks only
- Prefers a service that is fully managed and requires minimal effort from internal teams
- Is facing challenges in recruiting highly skilled cybersecurity professionals, and needs a partner that can provide expertise on-demand
- Prefers to have human analysts investigate and respond to security incidents
Choose XDR if your organization:
- Requires threat detection and response across multiple layers, including endpoints, networks, and cloud services
- Needs comprehensive visibility into security incidents across the entire infrastructure
- Wants to automate threat detection and response processes
- Wants to leverage AI and machine learning to improve threat detection and response efficiency
Additional managed services
Here are some other ways our experts can uncover your risks.
Real-time visibility into threats across your extended (cloud and on-premise) IT landscape.
Threat detection, analysis, and accelerated response to advanced, credential, insider and ransomware attacks.
Keeps your data and credentials safe in the cloud, data center, enterprise networks or IoT devices.